Quantum computing is poised to quickly turn a mindset of “we’re in good shape right now” into “why didn’t we start preparing sooner?” This is especially true when “now” refers to the encryption protecting customer data, intellectual property and the secrets a company’s board assumes are safe. Today’s widely used public-key systems were built for classical computers. A cryptographically relevant quantum machine could change the math fast, potentially wiping out the protections built over years of security planning.
That’s why the quantum conversation is shifting from tech experts’ speculations to plain business risk management. Data has a shelf life, and for a lot of organizations, it’s a long one. Contracts, health records, financial history, M&A documents and source code don’t become innocuous just because the quarter ended. Add in the “harvest now, decrypt later” reality—adversaries collecting encrypted traffic today and unlocking it later—and the timeline to address quantum risk shrinks. The urgency is also being reinforced by credible signals that the transition is already underway, including NIST’s finalized post-quantum encryption standards.
The good news is that organizations don’t need a quantum lab to start getting ready. But they do need clarity on where cryptography lives, how quickly it can be upgraded without breaking business processes, and who owns the decision-making when trade-offs emerge. Here, members of the Senior Executive Cybersecurity Think Tank weigh in on what organizations should do now to assess cryptographic vulnerabilities and build real crypto agility.
“Preparation isn’t about prediction. It’s about being ready when disruption stops being theoretical and quantum shifts are no longer academic.”
Assess Your Risk and Crypto Agility
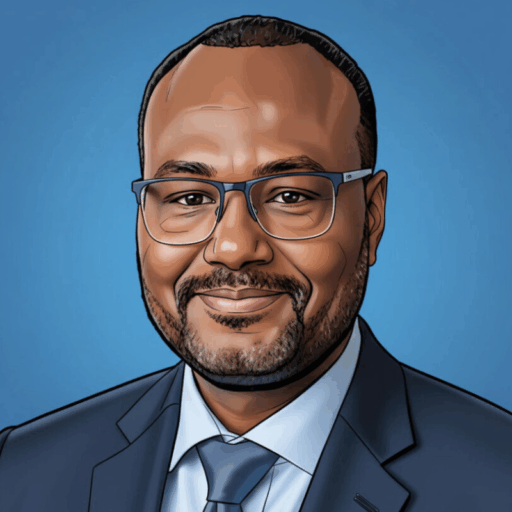
If quantum risk feels abstract, that’s usually a sign an organization doesn’t fully understand what assets need to be protected. Maman Ibrahim, Founder of Ginkgo Resilience LTD, says gaining full visibility into current cryptographic systems is an essential first step.
“The first risk is blindness,” he says. “Organizations need to start with a cryptographic inventory: what algorithms are in use, where and for what purpose.”
Such an inventory is not an academic exercise. It’s how teams find the places where future quantum capability could hit hardest. Ibrahim explains that the next move after cataloging is triage.
“Assess which systems rely on vulnerable algorithms like RSA or ECC and whether those systems support crypto-agile updates,” he says.
But what does it mean to be “crypto-agile”? Ibrahim offers a definition that keeps the focus on operations, not theory: “Crypto agility means building infrastructure that can swap algorithms without breaking operations.”
Ibrahim makes it clear that crypto agility means more than undergoing a technical refresh. It’s also not an initiative that can be dropped into IT’s lap and forgotten.
“It’s not a tech issue; it’s a governance one,” he explains. “Leadership should assign ownership, set timelines and integrate crypto review into change management.”
Ibrahim also offers a reality check for organizations that still view quantum as a distant threat or are tempted to wait for perfect clarity, complete tools or finalized guidance.
“Post-quantum threats may feel distant, but migration takes years. Waiting until standards are finalized is a mistake,” he warns. “Preparation isn’t about prediction. It’s about being ready when disruption stops being theoretical and quantum shifts are no longer academic.”
“Apply the 80/20 rule: Focus first on crown-jewel systems where exposure would cause the biggest financial, legal or reputational hit.”
Don’t Panic; Prioritize and Prepare
Scott Alldridge, President and CEO of IP Services, stresses that the time for organizations to act is now.
“Quantum computing isn’t sci-fi anymore; it’s a freight train we can already hear coming,” he says. “The data you encrypt today may be tomorrow’s low-hanging fruit for adversaries harvesting now to decrypt later.”
Still, Alldridge says, the right move isn’t to panic but to prepare.
“Start by assessing your ‘cryptographic debt,’” he advises. “Inventory where encryption lives across VPNs, TLS, PKI, databases, backups and the IoT.”
Quantum readiness can be overwhelming if teams try to fix everything at once. Alldridge pushes against that reflex, recommending a risk-focused plan for prioritization.
“Apply the 80/20 rule: Focus first on crown-jewel systems where exposure would cause the biggest financial, legal or reputational hit,” he says.
From there, Aldridge turns to adaptability, emphasizing the importance of building in the ability to change algorithms without rewriting major systems.
“Build crypto-agility into your design so algorithms can be swapped without major rewrites,” he says. “Centralize key management, avoid hardcoding crypto choices, and track NIST PQC guidance.”
An essential last step? Making sure systems and teams really are ready for the challenges ahead.
“Run tabletop exercises on ‘quantum day one’ to see if you’d scramble or stand ready,” Alldridge recommends. “The goal is to make quantum readiness part of your cybersecurity strategy today, not an emergency tomorrow.”
“The framework must be applied across your enterprise, including operations, sales and governance.”
Make Crypto Agility Everyone’s Mission
In some scenarios, pursuing cutting-edge technology upgrades can wait—or even be avoided. But Umang Modi, Managing Principal and Chief Strategy Officer at TIAG, says that “replacing vulnerable algorithms isn’t going to be an option.” He emphasizes detailed planning with clear intent.
“Future-proofing requires creating and following a strategic roadmap that includes a comprehensive cryptographic audit, risk prioritization and the implementation of a crypto-agile framework,” Modi says.
He notes that crypto agility fails if it’s treated as a security-only initiative that the rest of the business disregards or views as optional.
“The framework must be applied across your enterprise, including operations, sales and governance,” Modi stresses.
He underpins the urgency with reasoning even non-tech-savvy leaders can grasp: It’s important to start now, not because quantum risk will be “real” tomorrow, but because effective enterprise change takes time, coordination and repeatable processes.
“Taking proactive steps now is critical to rapidly adapting with minimal disruption,” Modi says.
Quantum-Prep Moves To Make Now
- Build a cryptographic inventory before you try to fix anything. Map what algorithms are in use, where they sit and what they protect so you can spot vulnerable dependencies and blind spots early.
- Treat crypto agility as a governance decision, not just an IT upgrade. Assign ownership, set timelines and fold crypto review into change management so the work survives beyond a single project cycle.
- Prioritize your crown-jewel systems using an 80/20 approach. Focus first on the assets where exposure would cause the biggest financial, legal or reputational hit, then expand from there.
- Design for algorithm swaps by centralizing key management and avoiding hardcoded crypto choices. Make it easier to transition as guidance evolves by reducing brittle integrations and keeping cryptographic decisions configurable.
- Run “quantum day one” tabletop exercises to test whether you’d scramble or stand ready. Use the exercise to expose decision gaps and unclear ownership, and upgrade bottlenecks while the stakes are still manageable.
- Build a strategic roadmap that makes crypto agility an enterprise-wide mission. Apply the framework across operations, sales and governance so quantum readiness is supported by the whole organization, not just the security team.
The Best Time to Build Crypto Agility Is Before You Need It
Quantum risk is still evolving, but the groundwork needed for readiness is not a mystery: Get visibility into where cryptography lives, prioritize the systems that matter most, and make crypto agility a governed capability rather than a last-minute scramble. Organizations that treat cryptography like managed infrastructure will adapt faster and be stronger when change arrives.
The implications go beyond swapping algorithms. As standards mature and attackers bet on “harvest now, decrypt later” tactics, crypto agility becomes a business resilience issue that touches ownership, budgeting, vendors and change management. The organizations that start now will be able to move deliberately later, while others may find themselves trying to modernize encryption under pressure, with higher risk and higher cost.